Enter the COCO
The techies might soon outnumber everyone else in the CSuite. Who should be worried? In the beginning was the CIO. The CIO was responsible for information and technology that supported the company's...
Read MoreExpert analysis and commentary on the evolving digital battlefield
The techies might soon outnumber everyone else in the CSuite. Who should be worried? In the beginning was the CIO. The CIO was responsible for information and technology that supported the company's...
Read More
Cybersecurity Goes to the Boardroom: Why NIS2 Changes Executive Liability and Why U.S. Companies Should Care Executives used to be able to ignore cybersecurity. That era is over. Europe's Network and...
Read More
Over 10 years ago, I worked for a very large web of corrupt and incestuous devopsfirst companies which positioned a front row seat to the beginning of the ever famous hype machine pitch: "Devops will...
Read More
The Data Breach Every American Should Know About Within a database that has over 4 million records, what do you think the most common name is? What is the most common birthday? The least? What is the...
Read More
When "Looks Real" Isn't Real An Expanded Analysis of the Emerging Synthetic Media Threat Landscape and Zero Trust Countermeasures Expanded Analysis Based on DrZeroTrust Research Version 1.1 ...
Read More
In cybersecurity, trust is currency. Every tool we deploy — whether a firewall, endpoint agent, or monitoring platform — represents an extension of our defense posture. But what happens when the very...
Read More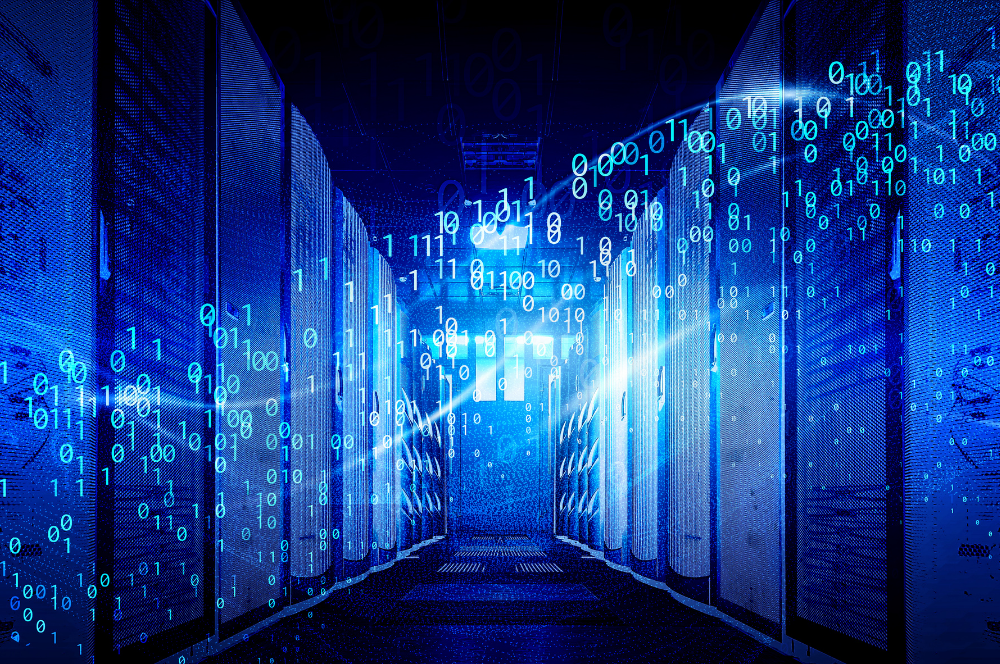
When people talk about cybersecurity, the conversation usually jumps to firewalls, encryption, or multifactor authentication. All important, but one of the simplest and most powerful habits often...
Read More
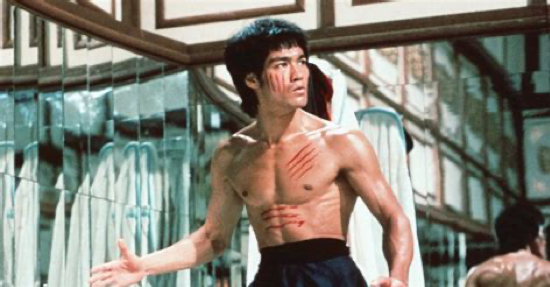
No locks can keep bad actors out forever There's no such thing as security. We may lock our cars when we leave them, but nothing can stop a robber who's determined to enter your vehicle. Every device...
Read More